MinSpærring servicen er en national service til administration og verifikation af en borgers samtykke og spærringer for sundhedsfagliges adgang til data i nationale systemer.
Formålet med dette dokument er beskrive arkitektur og design i MinSpærring servicen.
For et overblik over systemet se afsnittet "Overblik over løsningen".
I dokumentet bruges begreberne autorisation og autoriseret primært i en sikkerhedskontekst, det vil sige i forståelsen af, at en person eller et system er autoriseret til at bruge en given ressource. Hvis begreberne anvendes om en sundhedsfaglig med dansk autorisation, der er anført i Sundhedsstyrelsens autorisationsregister, vil det blive udtrykkeligt angivet.
| Version | Date | Responsible | Description |
|---|---|---|---|
1.0 | 29.06.2012 | Systematic | First edition |
1.1 | 28.11.2014 | Systematic | References to National Patient Index (NPI) removed |
1.2 | 25.11.2016 | Systematic | MinLog now reuses SOSI ID-card and no longer requires HSUID (5.4) |
1.3 | 7.2.2017 | Systematic | Added handling of data specific consent by precautionary principle to section 5.3.1. |
1.4 | 13.06.2018 | Systematic | Migrated to NSPOP SVN |
| 23.10.2018 | KIT | Document moved from Word to Confluence. Original document name was: SDD0011 Consent Services Architecture and Design.docx | |
| 14.05.2020 | KIT | SDS-3883 Etablering af IDWS snitflade | |
| 09.11.2020 | KIT | SDS-3685 Min Spærring skal anvende SORES til SOR-SHAK opslag | |
| 12.11.2020 | KIT | Oversættelse til dansk |
Formålet med dette afsnit er at give en oversigt over definitioner og dokumentreferencer, der bruges i dette dokument.
| Definition | Description |
|---|---|
NSI | National Sundheds IT |
NSP | National Service Platform |
| Reference | Beskrivelse |
|---|---|
Behov | National consentservice, v1.1 (behovsbeskrivelse for Min Spærring Service) |
Data Model | MinSpærring - Data Model |
Administra Service Interface Beskrivelse | MinSpærring - Administration Service Interface Description |
Verifikation Service Interface Beskrivelse | |
Driftsvejledning | |
MinLog | Snitfladebeskrivelse Min-log Web services (SSE/11734/IFS/0003) (Min-log Service Interface Description, available in Danish only). |
UdviklerGuide | |
HSUID-Header | MinSpærring - Healthcare Service User Identification Header Interface Description |
Sundhedsloven | LBK nr 913 af 13/07/2010 (Sundhedsloven) https://www.retsinformation.dk/forms/r0710.aspx?id=130455 |
Ændring af sundhedsloven | LOV nr 605 af 14/06/2011 (Lov om ændring af sundhedsloven) |
Grundlaget for samtykke service er som følger::
”The health act contains stipulations regarding a citizens’ right to decline retrieval or disclosure of information. In regard to electronic retrieval of patient information, the patient must be briefed about his right to decline retrieval, but it is not required that the patient’s consent is requested on the actual retrieval. In the remarks to the law, it is stated that this right must be supported electronically in new IT solutions, i.e. the patient or a health professional acting on behalf of the patient must be able to mark which information to which access is declined.
…
The consent service that is developed in connection with the NPI (National Patient Index) project should be viewed as the first draft. The consent service must be shared between NSP and the Health Journal and should consequently be developed in collaboration with Sundhed.dk and the architecture should support future extension of interface and functionality.
Specifically, the consent functionality in the NPI project must contain the following components:
A database with a simple data model for storage of negative and positive consent
Web Service for registration and lookup / control of consent information.”
Kravene, som MinSpærring skal opfylde, er uddybet i [Behov]. Det juridiske grundlag er beskrevet i [Sundhedsloven] med rettelser givet i [Ændring af sundhedsloven].
MinSpærring udstiller to services. Det er MinSpærring Administration og MinSpærring Verifikation.
Allows registration and maintenance of submitted consents for the citizen. The service expose the following operations
Tillader registrering og vedligeholdelse af spærringer og samtykker for en borger. Serivcen tilbyder nedenstående funktionalitet.
ConsentRegistrationsGet – Returnerer alle registreringer for en borger.
ConsentAdd – Opretter en ny spærringer eller samtykke for en borger. Et registrering er defineret i MinSpærring - Data Model og indeholder:
Type (samtykke eller spærring)
Hvad det gælder
Hvem det gælder for
Gyldighedsperiode
Operationen kan kaldes af både borgere og af en anden person, som det kaldende system har verificeret, har lov til at oprette en spærring eller samtykke på borgerens vegne.
Operationen understøtter desuden oprettelse af samtykke til udenlandsk sundhedspersonales adgang til data.
Nogle operationer tillader at bruger og borger ikke er den samme person. Hvis de ikke er den samme person logges handling til borgerens MinLog.
MinSpærring Administration opbevarer i sin database information om samtykke og spærring, som angivet af ConsentAdd ovenfor, ud over oplysninger om, hvem og hvornår samtykke henholdsvis oprettes og ændres.
Servicen anvendes til at verificere spærringer og samtykker mellem border og sundhedsfaglig. Service udstiller nedenstående operationer:
ConsentForUserCheck – Returnerer det generelle samtykkeforhold (samtykke eller spærring) for en bruger med hensyn til en borger; hvis brugeren har lov til at se alt eller intet om borgeren.
ConsentForDataCheck – Returnerer det specifikke samtykkeforhold (samtykke eller spærring) for en bruger og konkrete oplysninger om en borger; hvis brugeren har lov til at se disse konkrete oplysninger om borgeren. De konkrete oplysninger / dokumenter returneres i form af en liste af ID'er. ID'erne der ønskes undersøgt er en del af forespørgslen til servicen.
ConsentForForeignersCheck – Returnerer, om udenlandske sundhedsfaglige kan få adgang til patientoversigt og elektronisk recept til borgeren gennem epSos
Sammen med det kalende anvendersytem følger MinSopærring Verifikation følgende beslutningsgraf for at bestemme en borgeres / sundhedspersonale adgang til data:
![]()
Figur 1 Tilstandsdiagram for den oprindelige beslutning om at give adgang til sundhedsoplysninger om borgerne.
For en borger verificeres det kun at borgeren er godkendt og egne data kan tilgås.
For sundhedsfaglige er det nedenstående beslutningstræ der anvendes til at lave MinSpærring Verifikation:
![]()
Figur 2 Tilstandsdiagram for trin til bekræftelse af samtykke eller spærring, når en sundhedsfaglig forsøger at tilgå sundhedsoplysninger om en birger. Henvisninger i parentes henviser til [Sundhedsloven].
Bemyndigelse er en tilstand hvor en sundhedsfaglig arbejder på vegne af en anden. Den sundhedsfaglige der arbejdes på vegne er typisk ansvarlig for de handlinger der udføres.
Begge services overholder Den Gode Web Service 1.0.1 og kræver:
At anvendersystem er godkendt af STS på NSP med mindst sikkerhedsniveau 3
At anvender er whitelisted i servicen
Det er anvendersystemets ansvar It is the responsibility of the calling system to ensure that the user is authenticated and authorized.
Som afbildet i figur 3 lagres MinSpærring data i en central database, der replikeres til de forskellige NSP instanser.
MinSpærring Administration installeres på en central server og eksponeres på NSP-forekomster gennem afkoblingskomponenten DCC. Proxyen for MinSpærring Administration, der bruges i en NSP-instans, implementeres ikke som en del af denne service. Proxyen oprettes på NSP i form af en konfiguration af DCC.
MinSpærring Verifikation er kun installeret på cNSP og forespærger på den lokale database.
Systemet skal designes i overensstemmelse med de mål og prioriteter, der er angivet i tabel 1. Prioriteten for hvert mål er angivet med en score på 1 til 5, hvor 5 angiver den højeste prioritet.
| Mål | Prioritet | Kommentar |
|---|---|---|
Korrekthed | 5 | Den overordnede funktionalitet vedrører patientsikkerhed og er underlagt en omfattende juridisk ramme, som det er vigtigt at overholde |
| Pålidelighed | 2 | Hvis systemet ikke kan udføre sin opgave, skal fejlen videresendes. |
| Anvendelighed | 1 | Der er ingen brugergrænseflade. |
Sikkerhed | 4 | Systemet håndterer patient data. |
| Ydelse | 3 | De specifikke ydelseskrav er ikke kendt, da systemets belastning er ukendt, men ydeevne er blevet prioriteret, da systemet kaldes fra en del anvendersystemer og systemets ydelse vil derfor påvirke de kalende systemer. |
| Vedligeholdelse | 4 | Løsningen vil helt sikkert blive genstand for yderligere udvikling. Omkostningerne ved dette skal holdes lave. |
Fleksibilitet | 1 | Løsningen består af webservices. Dette resulterer i den nødvendige fleksibilitet i det samlede system. De enkelte services behøver ikke at være fleksible. |
Testbarhed | 3 | Løsningen skal kunne testes gennem automatiske tests, da der ikke er nogen brugergrænseflade. |
Portabilitet | 1 | De grundlæggende teknologiske beslutninger er taget på forhånd. |
Genbrugelighed | 2 | Komponenterne skal bruges gennem delegering - ikke ved genbrug af kode. |
Interoperabilitet | 2 | The desired interoperability is obtained through Web service interfaces |
Tabel 1: Design mål og deres indbyrdes prioritering
Dette afsnit indeholder vigtige designbeslutninger og deres begrundelse. Hvis det er relevant, præsenteres afviste designs også med begrundelsen for deres afvisning.
Fejlr og debug logging er implementeret via log4j der er konfigureret for hvert service. Der laves en logfil pr. service.
I denne log registreres exceptions og stacktraces. Hvis konfigurationen er indstillet til 'debug'-niveau, logges der også flowID ved ind- / udgang af servicemetoderne.
Debuglog er blevet implementeret for at lette fejlfinding, således at flowID (og følgelig en besked) kan spores mellem serviceopkald.
Service Level Agreement (SLA) logning håndteres via SLALOgning i NSPUtil biblioteket.
SLA-logging logger alle kald til de to service og består blandt andet af:
Tidspunkt, navn på den kaldte metode, eksekveringstids samt message ID.
Audit logging sker også via log4j via kategorien ”audit”. Audit logging skal logge
Tid (zulu time)
Bruger ID
Metodekald
borgeren
Anvender systems CVR nummer
SessionID fra IDWS sikkerhedskontekst (messageID)
The service configuration is performed in two (three for the administration service) different properties files that must be deployed on the Web server somewhere in the application’s classpath.
Servicekonfigurationen udføres i to (tre for MinSpærring Administration) forskellige property filer, der leveres som en del af docker setup.
Changes in the configuration should prompt a reboot of the service, as the configuration is loaded and verified on start-up of the individual services.
Ændringer i konfigurationen skal medføre en genstart af den container som servicen den kører i da konfiguration indlæses ved opstart.
For beskrivelse af konfigurationen se MinSpærring - Driftsvejledning.
Applikations konfiguration
Applikationen er konfigureret i filerne ConsentAdministration.properties og ConsentVerification.properties.
Al konfiguration af sikkerhed og serviceopsætning findes i disse filer.
Derudover angives placeringen af logkonfigurationsfilen og serviceklientkonfigurationen.
På denne måde er det muligt at konfigurere logning og klientopsætning uafhængigt af tjenesten, f.eks. om genbrug af logkonfigurationen mellem services.
Service klient konfiguration
MinSpærring Administration service skal være i stand til at kommunikere med Min Log'-tjenesten, og konfigurationen af den anvendte serviceklient skal også udføres i en konfigurationsfil.
Placeringen af denne fil findes i applikationskonfigurationen.
Log konfiguration
In the log configuration file, error and debug log configuration is provided by stating a log4j-logger property with the name log4j.logger.dk.nsi.
I logkonfigurationsfilen leveres konfiguration af error og debug ved at angive en log4j-logger property med navnet log4j.logger.dk.nsi.
Database konfiguration
Both consent services must be provided with a data source with the name ’ConsentServiceDS’ that has access to the consent database described in [Data Model].
Begge MinSpærring services skal forsynes med en datasource med navnet 'ConsentServiceDS', der har adgang til den database der er beskrevet i MinSpærring - Data Model.
Both services must have access to a data source with the name ’WhitelistDS’ that is used by whitelist validation of calling systems.
Begge tjenester skal have adgang til en datasource med navnet 'WhitelistDS', der bruges af whitelist af anvendersystemer.
The two consent Web services has been developed with a ”Java-first” approach, where the Java code has been developed independently and the WSDL generated at the time of running on the Web server on the basis of the implemented code.
The Java-first approach was chosen to ease development and maintenance of the service, as this makes it possible to harness existing Java-competencies. The option of customizing the exposed WSDL is sacrificed.
Contents of Web service call
The Web service operations consists of: a Medcom-header, a security-header, a HSUID-header [HSUID], and a body element.
In the consent administration, the contents of the HSUID-header is used to authenticate and validate the authorization of the calling user in addition to validate if the user is allowed to call the method with the included body parameters.
Furthermore, the ’acting user’-field in the HSUID-header is used to set the ’created by’ (’oprettet af’) and ’modified by’ (’modificeret af’) fields on consents in addition to assess if it must be logged that a consent has been created/changed by another citizen than the one the consent concerns.
In consent verification, only the validity of the HSUID-header is validated.
The Medcom-header is used to validate the security level and the signature.
The security header is used to validate whether the attached signature and STS security-token is valid, cf. the configuration that has been used to configure the service.
All other parameters for the method calls are contained in the attached body for which content varies in regard to the individual operation (see [Consent Administration Interface Description] and [Consent Verification Interface Description]).
Each service is implemented as a Java EE stateless session bean that implements an interface that defines the methods the Web service exposes. Both the bean and the Web Service implementation is handled through Java EE annotations.
By implementing the service as a Java EE bean, it is made possible for the application server to handle data source injection, transactions, and system resources, rather than handling this manually in the code.
Every aspect of complying with DGWS, IDWS, security handling and logging is handled by Java EE interceptors that are automatically invoked by the surrounding EJB container.
The consent database handling is implemented through Hibernate, which makes it possible to detach the database handling from the code. The data source for the consent database is handled through injection from the EJB container in the application server.
The data source for the whitelist (that is used to verify whether calling systems has access to the service), is handled by a context-lookup in the code and thus is not injected from the EJB container.
The reason for doing so is that the whitelist is not handled directly by the bean, but by an interceptor that can be configured independently of the bean implementation. The interceptor is provided by a common code module and is used by multiple services to ensure that DGWS is obeyed in addition to validation of security. To avoid a dependency from the whitelist to the bean, the data source lookup takes place in the shared module.
The data model for consent service is documented in [Data Model].
This section describes static as well as dynamic aspects of the system architecture, including the basis for the individual design choices.
The general service structure is that the service is implemented as a stateless session bean that implements a Web interface that is a Java Web service.
This bean then handles the service logic, DAOs and other business logic.
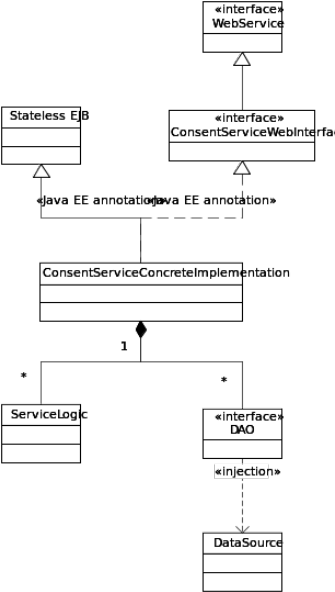
Security validation, logging and error handling is handled by a number of Java EE interceptors.
The service is deployed on an application server that is responsible for generation of a Web interface (and WSDL), managing data source injection and handling of system resources.
The database communication is handled by a number of DAOs (one per injected data source) that encapsulates the database communication in a number of object related methods.
The whitelist is not handled through a DAO. Instead, the whitelist implementation makes a direct request to its data source.
ConsentVerificationDAO
Is handled by an entity manager (defined in the persistence.xml-file in the application) named ’ConsentVerificationService’ that is injected through the Java EE annotation @PersistenceContext in the bean.
This entity manager make use of the data source ’ConsentServiceDS’.
The DAO exposes methods that correspond to the functions that the Web service expose to calling systems. It is used by the bean to obtain a citizen’s consents.
ConsentAdministrationDAO
Is handled by an entity manager (defined in the persistence.xml-file in the application) named ’ConsentAdmin’ that is injected through the Java EE annotation @PersistenceContext in the bean.
This entity manager make use of the data source ’ConsentServiceDS’.
The DAO exposes methods that correspond to the functions that the Web service expose for calling systems. It is used by the bean to modify the citizen’s consents.
The database operations are implemented by means of the Hibernate framework.
A number of interceptors are used in the implementation of the specific service for performing SLA-logging, error handling and security validation. These interceptors make use of the interceptor-pattern and prevents the EJB container from calling the specific service implementation directly, as the call hits a proxy that calls the annotated interceptors sequentially.
Each interceptor then wraps the ensuing call and can perform error handling and logging.
Every interceptor is annotated with @AroundInvoke, which means that they are called before the service methods are invoked.
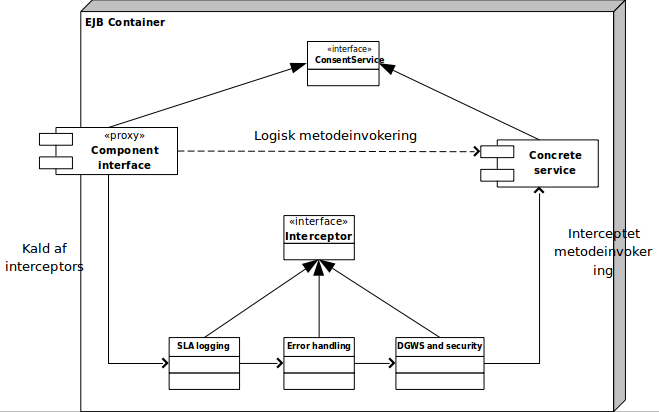
SLA logging
SLA log-interceptor is responsible for SLA logging of all service calls.
Error handling
Consent Administration and Consent Verification handles errors differently. See the subsections "Error Handling" in the following two sections.
The service logic is implemented directly in the bean implementation as the logic primarily consist of forwarding calls to the DAO. Additionally, overall validation of the HSUID header is performed in addition to validating that health professionals are only allowed to call the ‘ConsentAdd’ method.
If the user differs from the citizen that is subject of the consent, a call is additionally made to the Min-log service to log this change in the citizen’s ’Min Log’.
The consent service make use of the Min Log service client (see section 5.4).
Error handling
The error handling intercept performs general error handling of all service calls and wraps and ensures that it is only SOAP faults that are returned to the calling systems.
It additionally ensures that potential errors are logged in the error log and performs debug logging of flow ID.
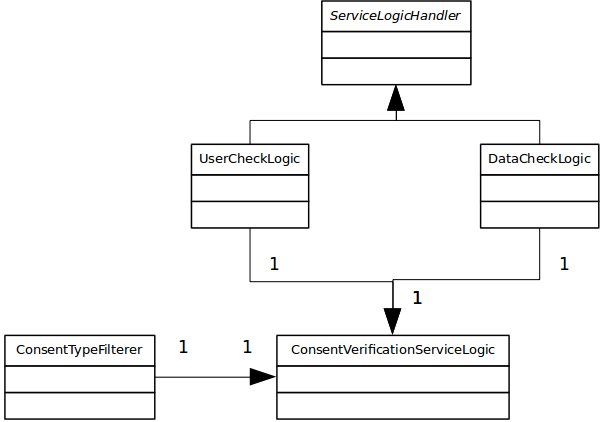
The service logic comply with the decision graph that has been made for consent verification (see section 2.2) and it is implemented in the class ConsentVerificationServiceLogic.
Consent verification
The verification consists of three different operations: user verification, data verification and verification of foreign health professionals.
The foreign health professionals are persons who attempt to access a citizen’s data through epSos. It is possible for a citizen to register positive consent for this (see section 2.2).
User verification is used to obtain an indication of whether a user can access a citizen’s data. It is possible for a system to call this service and thus avoiding examination of each individual data element.
If ’Positiv’ is returned, then the calling system do not need to validate consent for possible data as the citizen has provided consent for the calling user for all data.
If ’Negativ’ is returned, then the calling system do not need to lookup data, as negative consent is provided for the calling user for all data.
Only on a ’Dataspecifik’ returnvalue will it be necessary for the calling system to make a request to the other verification method.
Data verification is used to examine which data in a sequence of specific data elements the user has consent too view.
This method is only necessary to call if user verification has returned a data specific result.
The method accepts a list of possible data elements and returns a list of those data elements (from the received list) that the user has consent to view.
The service logic class retrieves all the citizen’s consents from the database and filter these using the class ConsentTypeFilterer.
In this class, consents are filtered in relevant units corresponding to the various steps in the decision graph (e.g. positive consent for the user’, ‘negative consent for all’, ’positive consent for the users organization’ etc.). The filtration is performed on the consents and possible associated ’who’ element. The ‘what’ element is not examined in the filtration.
Lookups are performed in the SORES service to sort organization-specific consents correctly.
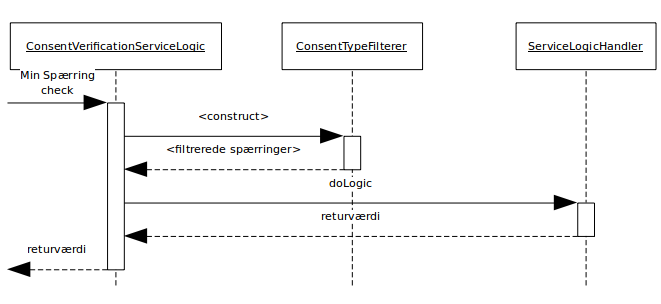
If user or data verification is performed, then the general consent verification logic will subsequently be performed in the abstract class ServiceLogicHandler that has been implemented by two concrete classes: a class for user verification and a class for data verification. Filtration of consents, order of consent verification, and handling of positive/negative/data specific consents, are identical for both the concrete classes.
General service verification
The general verification algorithm is as follows, where the parenthesized text indicates if the individual step results in a positive, negative or data-specific handling.
In each step, it is examined whether the filtration has found consents that belong to the current category whereupon the stated handling is performed.
For instance, a positive handling is performed if a positive consent is found for the current user in step 2.
’On behalf of’ (step 1) is used when a health professional is working on behalf of another health professional. This could be a medicine student working on behalf of his senior physician or a secretary making lookups for a health professional.
In this case, the algorithm is swiftly executed if positive consent exists towards both users. Otherwise, it is required that if negative consent exists towards only one of the users, no access is allowed to the user’s data.
On behalf of (positive/negative/data-specific)
Positive personal consent for all (positive)
Positive personal consent for specific data (data-specific)
Negative personal consent for all (negative)
Positive consent towards the user’s organization for all (positive)
Positive consent towards the user’s organization for specific data (data-specific)
Negative consent towards anybody for specific data (data-specific)
Negative consent towards anybody for all (negative)
No more consents / no consents registered (positive)
Handling of the individual steps varies between user and data-verification.
User verification
The logic for user verification is simple and will result in either a positive, negative or data-specific answer.
The value for the first handling, where consents are found in the database, is returned to the calling system.
’Positive’ is returned when consents are found in a positive step (2, 5), ’Negative’ in the negative steps (4,8) and ’Data-specific’ in the data-specific steps (3,6,7).
In step 1, a value is returned that depends on the citizen’s consents towards the person that work is performed on behalf of, and the user calling the service.
Data verification
Consent verification for data sorts the data, where there is negative consent, from the total list of possible data elements. The verification is performed once for each data element.
If positive handling is performed, the element is added to the return list. If negative handling is performed, the element is removed from the list of possible data elements
On a data-specific handling, iteration is performed over the remaining possible data elements and the ’what’-elements of the consents are examined. Comparison is made with the creating organization of the data element and the ’what’-organization provided in the consent:
If no ’what’-element is provided or the ’what’-organization is subject of a positive consent, the element is added to the return list.
If it is the subject of a negative consent, it is removed from the list of possible data elements.
Handling by precautionary principle:
If the creating organization of the data element is of type unknown or other, it is removed when there is negative consent or one or more negative data specific consents with overlapping referral period, unless there is also a positive data specific consent (with overlapping referral period) which applies to any origin (‘what’-organization).
If the creating organization of the data element is of type SHAK or DEA (Danish: ydernummer) and the identifier cannot be looked up as a SOR code, it is treated similarly to the unknown or other organization type described above.
Otherwise, verification continues.
This proceeds until all steps of the verification has been passed or the list of possible data-elements is empty.
The return list (with all the data elements without negative consent) is returned to the calling system.
The handling by precautionary principle is simply, that if a data element is of type unknown or type other, it might represent data from the same organization (‘what’-organization) as that of a negative data specific negative consent. The data element, therefore is eligible for being removed from list. The same does not apply for the positive data specific consent. Although the data element might represent the same organization, the opposite might as well be true. Therefore, positive data specific consent applies only when defined for any origin (any ‘what’-organization).
Error handling
The error handling intercept performs general error handling of all service calls and wraps and ensures that it is only DGWS faults that are returned to the calling systems.
It additionally ensures that potential errors are logged in the error log and performs debug logging of flow ID.
DGWS and security
The DGWS-interceptor performs validation of the security and Medcom headers. It ensures that only authenticated user systems can access the service by authorizing them in a whitelist.
On verification of foreign health professionals, iteration occurs over all the citizen’s consents to examine if one exists towards foreign health professionals (epSos).
If so, the type of the consent is returned (positive/negative). Otherwise, negative is returned, as the citizen specifically must allow access for foreign health professionals.
All calls to the Min-log service is performed through the Min-log service client, based on the loaded configuration (see section 3.2.2).
Call is forwarded to the Min Log service with the same Medcom and security headers, as received by the calling system.
The interface for the Min-log service can be seen in [Min-log].
There is no specific sequence in which the two components must be integrated. However, the Min Log service-client must be available before the consent administration service can be integrated.
For a description of the build process and external/internal depencies for the service, see [UdviklerGuide].
To be able to test the consent administration service, the Min Log-service must be available. It is also possible to test consentadministrationsservicen with a stub for Min Log.
Min Spærring administration
The following three integration test classes exists for the administration service:
The security-class ensures that the service validates and verifies those security tokens that are included in the service request.
The service-class contains those integration tests that verify that the service requirements have been met, in addition to ensuring that OIO-IDWS 1.1 and SLA-logging is implemented correctly.
The MinLog-class ensures that the service logging mechanism using MinLog is implemented correctly.
Consent verification
Two unit test classes exists for the verification service:
ConsentVerificationLogicTest and ConsentForForeignersTest
The verificationLogic-test ensures that the service logic classes has been implemented correctly.
The foreigners-test ensures that the logic that checks for consents for foreign health professionals has been implemented correctly.
Additionally, two integration test classes exists for the verification service:
ConsentVerificationServiceIT and ConsentVerificationSecurityIT
The security-class ensures that the service validates and verifies the security tokens that are included in the service request.
The service class contains those integration tests that verify that the service requirements have been met, in addition to ensuring that DGWS 1.0.1 and SLA-logging is implemented correctly
Common
Furthermore, there exists a number of unit tests that ensure that the different interceptor-validations and DAOs has been implemented correctly.