Introduktion
Dette dokument henvender sig til udviklere og arkitekter, der vil anvende samtykkeservice på NSP. Det antages, at læseren er fortrolig med webservices og de yderligere komponenter på NSP såsom STS, udover at have kendskab til Den Gode Webservice (DGWS).
Dokument historik
| Version | Dato | Ansvarlig | Beskrivelse |
|---|---|---|---|
1.0 | 29.06.2012 | Systematic | Initial version |
1.1 | 28.11.2014 | Systematic | References to National Patient Index (NPI) removed |
1.2 | 07.09.2016 | Systematic | Description of additional conditions for data specific consent check (paragraph 2.2) |
1.3 | 07.12.2016 | Systematic | Consent services now support DCC – (paragraph 3.1.1 and 3.1.2) Changed sts.endpoint to new endpoint in example properties file |
1.4 | 13.06.2018 | Systematic | Migrated to NSPOP SVN |
| 22.10.2018 | KIT | Document moved from Word to Confluence. Original document name was: PHB0035 Consent Services Users Guide.docx | |
| 12.11.2020 | KIT | Oversættelse fra engelsk til dansk | |
| 17.12.2021 | KIT | Tilføjet request/response eksempler for Samtykkeservicen Administration |
Definitioner og referencer
| Definition | Beksrivelse |
|---|---|
NSI | National Sundheds IT |
NSP | National Service Platform |
SHAK | SygeHusAfdelingsKode |
SOR | Sundhedsvæsnets Organisationsregister |
STS | Security Token Service |
| Reference | Beskrivelse |
|---|---|
DGWS 1.0 | Den Gode Webservice 1.0 |
DGWS 1.0.1 | Den Gode Webservice 1.0.1 |
HSUID-header | |
MinSpærring - Verifikation Service Interface Beskrivelse | Samtykkeservicen - Verifikation Service Interface Beskrivelse |
MinSpærring - Administration Service Interface Beskrivelse | |
Data Model |
Interface Beskrivelse
Snitfladerne for de to services er beskrevet i detaljer i dokumenterne Samtykkeservicen - Verifikation Service Interface Beskrivelse og MinSpærring - Administration Service Interface Description.
I dette afsnit er kun de enkelte komponenter, der er nødvendige for at beskrive brugen af de to tjenester beskrevet.
Fælles
Security header
For at kalde de to Samtykkeservicen services skal der anvendes et niveau 3 ID-kort udstedt af STS'en.
Det skal desuden sikres, at man har et angivet CVR-nummer og at dette er whitelisted i servicen. De to services bruger forskellige whitelisting tabeller, så CVR-nummer skal føjes til den ene eller begge, afhængigt af hvilken tjeneste man vil tilgå.
Der findes en admin-snitflade (til Samtykkeservicen administrationsservices), som er tilgængelig for sundhedspersoner, der er autentificeret med et niveau 4 ID-kort og som besidder den nationale rolle 'urn:dk:healthcare:national-federation-role:code:41001:value:SundAssistR1'.
Medcom header
I Medcom-headeren skal det sikres, at Flow-ID er sat korrekt. Hvis servicene kaldes fra et andet system der også anvender DGWS skal Flow-ID bevares fra dette opkald.
Medcom-headeren returneres fra alle operationer da den er indstillet som en ind / ud-parameter med flowstatus opdateret til 'afsluttet med succes'.
HSUID header
Hvis brugeren er en sundhedsfaglig person skal HSUID-headeren udfyldes med identifikation af den bruger, der udfører en given operation. Nogle af disse oplysninger genbruges muligvis i selve meddelelsen, og disse skal naturligvis være konsistente (jf. Samtykkeservicen - Verifikation Service Interface Beskrivelse og MinSpærring - Administration Service Interface Description). HSUID header skal ikke angives i admin-snitfladen og autentifikation og autorisation baserer sig udelukkende på oplysningerne i ID kortet.
Er det borgeren selv der ændre sine spærringer må HSUID-headeren gerne være tom (null) da de oplysninger der skal bruges fra headeren allerede findes i IDWS billetten.
Samtykkeservicen Verifikation
Samtykkeservicen Verifikation har to operationer til at verificere samtykke fra en sundhedsfaglig: ConsentForUserCheck og ConsentForDataCheck.
Formålet med ConsentForUserCheck-operationen er, at gøre det muligt for et brugersystem hurtigt at kontrollere, om en bruger har generelt samtykke eller generel spærring.
Hvis operationen vender tilbage positiv eller negativ, er det ikke nødvendigt at kalde yderlige for at afgøre om en sundhedsfaglig har lov til at tilgå data.
På et positivt svar antager brugersystemet, at brugeren har samtykke til at se sundhedsdata vedrørende den borger, som Samtykkeservicen databasen er ansvarlig for. Omvendt antages det på et negativt svar, at borgeren har oprettet en spærring vedrørende adgang til data.
Operationen ConsentForDataCheck accepterer en liste over metadataelementer og filtrerer dem baseret på borgerens samtykke eller spærring.
Hvis ID'erne er en SHAK-kode eller et Ydernummer forsøger verifikations servicen at slå de relaterede SOR koder op som vil blive anvendt i forbindelse med brugeresn spærring eller samtykke.
Derudover, hvis der er angivet en dataspecifikt spærring til en organisation, inkluderes de hierarkiske forældre til den organisation i dette samtykke. Medmindre der er givet et specifikt samtykke.
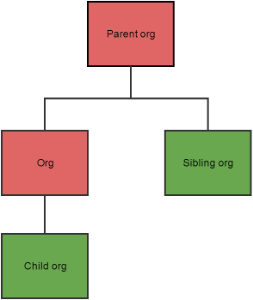
Dette illustreres i de følgende eksempler. Figur 1 viser borger, der har et generelt samtykke, men som har givet en dataspecifikt spærring til organisationen "Org". Hvis organisations id'er fra alle fire organisationer sendes til Samtykkeservicen Verifikation viser diagrammet svaret hvor rød er spærring og grøn er samtykke.
Figur 1: Spærring på ”Org” der har indflydelse på den overliggende organisation.
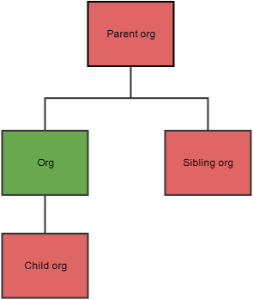
På den anden side, hvis borgeren har oprettet en general spærring og givet et specifikt samtykke til data fra "Org" for en given bruger, påvirkes overliggende organisation ikke. Se figur 2.
Figur 2: Specikt samtykke på ”Org” påvirker ikke overliggende organisation.
De ID'er der returneres fra servicen er de data som anvenderen har samtykke til at få vist.
It is the user systems responsibility to ensure that the used IDs are unique so that they can be distinguished in the returned list. The service does not use the IDs for anything else than the return list.
Det er anvendersystemets ansvar at sikre, at de anvendte ID'er er unikke, så de kan skelnes på den returnerede liste. Tjenesten bruger ikke ID'erne til andet end returlisten.
Samtykkeservicen Administration
Opret- rediger- og sletoperationer accepterer alle samtykke/spærring-objekter som parametre. Indholdet af et objektet vises i MinSpærring - Datamodel afsnit 2.
Alle metoder i administrationen af samtykke og spærringer tillader den borger, der opretter en registrering (eller sletter / ændrer), at være forskellig fra den borger, som registreringen vedrører.
Dette betyder, at en borger kan oprette / redigere / slette registretring på vegne af en anden borger, så længe borgeren har tilladelse til det.
Ligeledes er det muligt for en sundhedsfaglig at oprette et samtykke eller spærring (men ikke redigere eller slette) på vegne af en borger.
Det er brugersystemets ansvar, at brugeren er godkendt og autoriseret til at udføre en handling på vegne af en anden.
Admin-snitfladen er til brug for sundhedsfaglige til hjælp for ikke digitale borgere. Sundhedsfaglige har i denne snitflade adgang til alle administrative services: Opret, rediger, slet og hent.
Notificeringer i NAS
For alle ændringer af en borgers spærringer (oprettelse, opdateringer og sletninger), sker der en notificering via NAS få sekunder efter ændringen er gemt. Se evt. NAS 2.0 Anvenderguide.
De enkelte notificeringer indholder ikke detaljer vedr. opdateringen eller spærring, men udelukkende oplysninger om det cprnummer, for hvilket opdateringen har fundet sted. Det er efterfølgende op til anvenderen at hente ændringerne ud via snitfladerne.
Følgende er et eksempel på en opdateringsnotificering:
Topic der anvendes: http://sundhedsdatastyrelsen.dk/ConsentAdministration/2021/03/01:ConsentUpdated
Eksempler
I dette afsnit gives eksempler på, hvordan man kan bruge et Java-baseret systemet til at kalde de to services.
Kodeeksemplet er taget fra integrationstestene for servicen, og begge metodekald, variabler og parametre kommer fra integrationstesten.
Koden kan muligvis ikke være i stand til at kompilere eller køre i sin nuværende form, da den kun er beregnet som en guide til, hvordan man opretter et kald til tjenesten.
Eksempler på IDWS kald request og response
ConsentModifications
ConsentAddConstraint
ConsentAddPositive
ConsentRevoke
ConsentRegistrationsGet
Service Klienter
Der er udviklet en service klient til hver service. Klienterne kan findes som maven moduler.
<dependency> <groupId>dk.nsi.consentservices.verification</groupId> <artifactId>consent-verification-client</artifactId> <version><desired client version></version> </dependency>
og:
<dependency> <groupId>dk.nsi.consentservices.administration</groupId> <artifactId>consent-administration-client</artifactId> <version><desired client version></version> </dependency>
Oprettelse af service client
Disse serviceklienter konfigureres ved hjælp af en property fil, og klienten sørger for at få et gyldigt STS-token, indsætte korrekte headers osv.
Konfiguration af klienten sker via ClientConfig. ClientConfig's argument er navnet på den property fil der skal anvendes. Filen skal findes på classpath.
Koden nedenfor opretter en web service port til Samtykkeservicen Verifikation:
Config config = new ClientConfig("VerificationClient").
addRequiredKeys(ConsentVerificationService.CONFIG_KEY, ConsentVerificationService.CONFIG_ENDPOINT);
URL wsdl =
new URL(config.getProperty(ConsentVerificationService.CONFIG_KEY));
String wsendpoint = config.getProperty(ConsentVerificationService.CONFIG_ENDPOINT);
ConsentVerificationServiceservice =
new ConsentVerificationService (config, wsdl);
service.initialise();
ConsentVerification port = service.getConsentVerificationPort(wsendpoint);
Dette forudsætter, at en VerificationClient.properties-fil kan findes på classpath
Lignende kode skaber en klient til Samtykkeservicen Administration, klienten er bare klassen ConsentAdministrationService i stedet, og kaldet returnerer en web service port der er defineret i klassen ConsentAdministration.
Konfiguration
Den konfigurationsfil der gives til service klient skal definere en række properties som klienten anvender til at kommunikere med servicen.
administration.wsdl.location = http://localhost:8080/consent-administration/service?wsdl administration.service.url = http://localhost:8080/consent-administration/service verification.wsdl.location = http://localhost:8080/consent-verification/service?wsdl verification.service.url = http://localhost:9090/consent-verification/service idcard.level = 3 idcard.system.name = TESTSTS idcard.subject.id.type = medcom:cvrnumber idcard.subject.id = 19343634 idcard.subject.name = JERNALDERBYENS VENNER sts.test.mode = false sts.endpoint = http://test1.ekstern-test.nspop.dk:8080/sts/services/NewSecurityTokenService sts.token.expiry.threshold = 60 sts.keystore = jks/validVocesVault.jks sts.keystore.password = !234Qwer cert.expires.in.warning = 30
Værdierne er taget fra integrationstesten og skal tilpasses til det anvende systemet Det vil sige sti til certifikat, systemnavn osv.
Headers
Derefter kan service og port bruges til at oprette de nødvendige headers så det er muligt at kalde servicen.
Et flowID er angivet i headeren.
DGWSHeaderWrapper signedHeaders = service.getSignedHeaders(flowID); Holder<Header> medcomHeader = new Holder<Header>(signedHeaders.getMedcomHeader()); HsuidHeader hsuidHeader = createHsuidHeader();
Værdierne i HSUID-headeren skal sættes manuelt ved at kalde en metode, der opretter objektet (se MinSpærring Healthcare Service User Identification Header Interface Description for en beskrivelse af headerindholdet).
Medcom-headeren er pakket ind i et holderobjekt, da det er en request/response-parameter.
Eksempel på kald af Samtykkeservicen Verifikation
Et eksempel på kald af ConsentForDataCheck er vist her.
List<ConsentDataRegistration> consentData; // the list must be populated elsewhere ConsentForDataCheck consentForDataCheck = new ConsentForDataCheck(citizen, healthcareProfessional, onBehalfOf, organization, consentData); ConsentForDataResponse consentForDataCheckResponse = PORT.ConsentForDataCheck(consentForDataCheck, medcomHeader, signedHeaders.getSecurityHeader(), hsuidHeader);
Elementet consentData skal være en liste over ConsentDataRegistration-objekter, se MinSpærring - Administration Service Interface Beskrivelse.
Servicen returnerer en liste af ID'er som den sundhedsfaglige har samtukke til at få vist.
Eksempel på kald af Samtykkeservicen Administration
Her vises et eksempel på et kald til ConsentAdd i administrationsservicen. Indholdet af det faktiske samtykkeobjekt vises ikke her:
Consent consentItem = new Consent(); consentItem.setCitizenCPR(citizen); consentItem.setPositiveConsent(positive); consentItem.setValidFromDate(validFrom); consentItem.setValidToDate(validTo); consentItem.setWho(who); consentItem.setWhat(what); PORT.ConsentAdd(Arrays.<Consent>asList(consentItem), medcomHeader, signedHeaders.getSecurityHeader(), hsuidHeader);
Klient generering fra WSDL
Det er også muligt selv at generere en klient baseret på en WSDL.
Samtykkeservicen services versioner
Både den administrative og verifikationssnitfladen findes i flere versioner. Nedenstående liste er en fortegnelse over disse og deres endpoints og WSDL. Urlen skal tilpasses til det miljø, som anvenderen ønsker at ramme (se FAQ NSP miljøer).
| Verifikationsservice | URL | WSL |
|---|---|---|
| DGWS service til verfification af bruger og data | http://localhost:8080/consent-verification/service | http://localhost:8080/consent-verification/service?wsdl http://localhost:8080/consent-verification/service-contract/wsdl/consent-verification.wsdl |
| Administrationsservice | ||
| DGWS service til administration af spærringer | http://localhost:8081/consent-administration/service | http://localhost:8081/consent-administration/service?wsdl http://localhost:8081/consent-administration/service-contract/wsdl/consent-administration-dgws.wsdl |
| IDWS service til administration af spærringer | http://localhost:8081/consent-administration/serviceidws | http://localhost:8081/consent-administration/serviceidws?wsdl http://localhost:8081/consent-administration/service-contract/wsdl/consent-administration-idws.wsdl |
| DGWS service til administration af spærringer v2 | http://localhost:8081/consent-administration/service-2.0 | http://localhost:8081/consent-administration/service-2.0?wsdl http://localhost:8081/consent-administration/service-contract/wsdl/consent-administration-dgws-20201104.wsdl |
| IDWS service til administration af spærringer v2 | http://localhost:8081/consent-administration/serviceidws-2.0 | http://localhost:8081/consent-administration/serviceidws-2.0?wsdl http://localhost:8081/consent-administration/service-contract/wsdl/consent-administration-idws-20201104.wsdl |
| DGWS service til administration af spærringer for ikke digititale borgere | http://localhost:8081/consent-administration/service-adm-2.0 | http://localhost:8081/consent-administration/service-adm-2.0?wsdl http://localhost:8081/consent-administration/service-contract/wsdl/consent-administration-adm-20220207.wsdl |